BIFOLD Researchers Prof. Dr. Georgios Smaragdakis and Prof. Dr. Anja Feldmann, together with colleagues from Deutsche Commercial Internet Exchange (DE-CIX) and Brandenburg University of Technology, show that the exchange of information about ongoing cyberattacks has the potential to detect and mitigate substantially more attacks and protect critical parts of the Internet infrastructure. Their paper “United We Stand: Collaborative Detection and Mitigation of Amplification DDoS Attacks at Scale” was accepted at the ACM Conference on Computer and Communications Security (ACM CCS) 2021.

Our commercial and social activity is increasingly moving online. The ongoing pandemic is a reminder of how dependent we are on the smooth operation of online services such as e-banking, e-commerce, video streaming, video conferencing, and e-mail. Unfortunately, attacks on such critical services are at an all-time high. The so-called Distributed Denial of Service (DDoS) attack is a popular type of cyberattack that aims to make servers unavailable.
“At least once a week, we read in the news about a DDoS attack that shuts down online services of enterprises or the public sector. We are very frustrated that 20 years after the first DDoS cyberattacks, current solutions are not effective enough to mitigate such attacks.”, says BIFOLD Fellow Georgios Smaragdakis, Professor of Cybersecurity at TU Delft. The researchers collaborated with eleven network infrastructure operators, Internet Exchange Points (IXPs), in central and south Europe and the USA, which interconnect more than 2.100 networks.
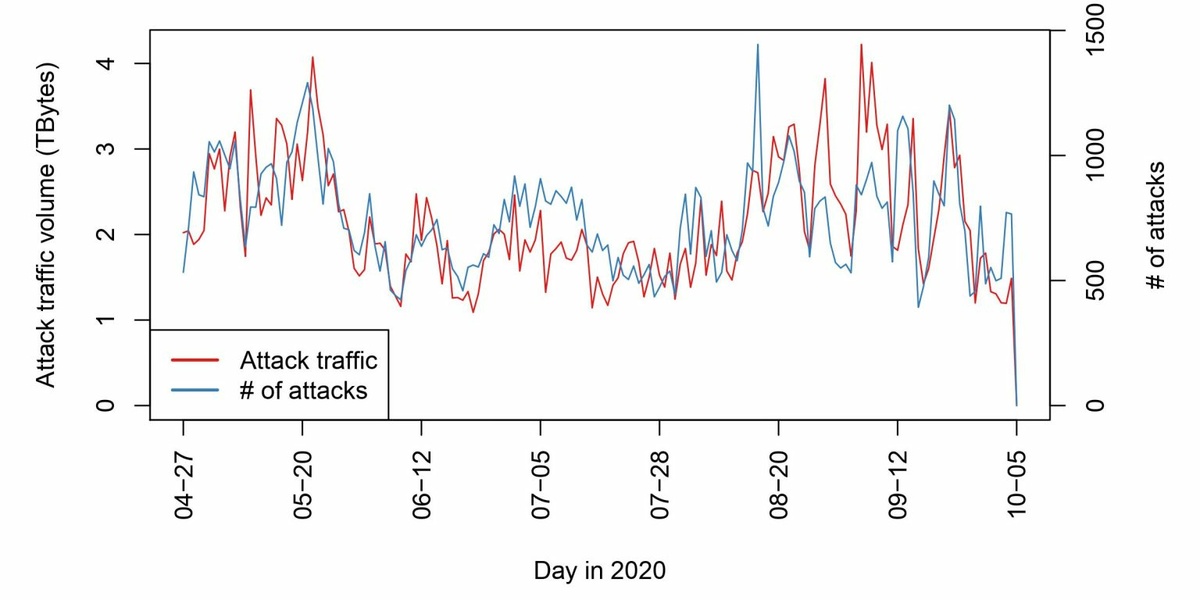
They developed inference techniques to detect DDoS cyberattacks and applied them on massive network data collected at the distributed vantage points over six months. In total, they detected and analyzed more than 120.000 cyberattacks. Their results show that between 500 and 1.500 DDoS cyberattacks with traffic of more than one Gigabit per second are observable every day. The total attack traffic reaches up to four Terabytes per day (see Figure). Unfortunately, 80 percent of these attacks are not detectable with current DDoS detection techniques applied locally at each site!
The publication in detail:
Daniel Wagner, Daniel Kopp, Matthias Wichtlhuber, Christoph Dietzel, Oliver Hohlfeld, Georgios Smaragdakis, Anja Feldmann: United We Stand: Collaborative Detection and Mitigation of Amplification DDoS Attacks at Scale. CCS 2021: 970-987
Abstract
Amplification Distributed Denial of Service (DDoS) attacks’ traffic and harm are at an all-time high. To defend against such attacks, distributed attack mitigation platforms, such as traffic scrubbing centers that operate in peering locations, e.g., Internet Exchange Points (IXP), have been deployed in the Internet over the years. These attack mitigation platforms apply sophisticated techniques to detect attacks and drop attack traffic locally, thus, act as sensors of attacks. However, it has not yet been systematically evaluated and reported to what extent coordination of these views by different platforms can lead to more effective mitigation of amplification DDoS attacks. In this paper, we ask the question: “Is it possible to mitigate more amplification attacks and drop more attack traffic when distributed attack mitigation platforms collaborate?”
To answer this question, we collaborate with eleven IXPs that operate in three different regions. These IXPs have more than 2,120 network members that exchange traffic at the rate of more than 11 Terabits per second. We collect network data over six months and analyze more than 120k amplification DDoS attacks. To our surprise, more than 80% of the amplification DDoS are not detected locally, although the majority of the attacks are visible by at least three IXPs. A closer investigation points to the shortcomings, such as the multi-protocol profile of modern amplification attacks, the duration of the attacks, and the difficulty of setting appropriate local attack traffic thresholds that will trigger mitigation. To overcome these limitations, we design and evaluate a collaborative architecture that allows participant mitigation platforms to exchange information about ongoing amplification attacks. Our evaluation shows that it is possible to collaboratively detect and mitigate the majority of attacks with limited exchange of information and drop as much as 90% more attack traffic locally.
Abstract
Amplification Distributed Denial of Service (DDoS) attacks’ traffic and harm are at an all-time high. To defend against such attacks, distributed attack mitigation platforms, such as traffic scrubbing centers that operate in peering locations, e.g., Internet Exchange Points (IXP), have been deployed in the Internet over the years. These attack mitigation platforms apply sophisticated techniques to detect attacks and drop attack traffic locally, thus, act as sensors of attacks. However, it has not yet been systematically evaluated and reported to what extent coordination of these views by different platforms can lead to more effective mitigation of amplification DDoS attacks. In this paper, we ask the question: “Is it possible to mitigate more amplification attacks and drop more attack traffic when distributed attack mitigation platforms collaborate?”
To answer this question, we collaborate with eleven IXPs that operate in three different regions. These IXPs have more than 2,120 network members that exchange traffic at the rate of more than 11 Terabits per second. We collect network data over six months and analyze more than 120k amplification DDoS attacks. To our surprise, more than 80% of the amplification DDoS are not detected locally, although the majority of the attacks are visible by at least three IXPs. A closer investigation points to the shortcomings, such as the multi-protocol profile of modern amplification attacks, the duration of the attacks, and the difficulty of setting appropriate local attack traffic thresholds that will trigger mitigation. To overcome these limitations, we design and evaluate a collaborative architecture that allows participant mitigation platforms to exchange information about ongoing amplification attacks. Our evaluation shows that it is possible to collaboratively detect and mitigate the majority of attacks with limited exchange of information and drop as much as 90% more attack traffic locally.


